Security in the machine
My recent reading of Seizing the Enigma: The Race to Break the German U-Boat Codes, 1939 – 1943—by David Kahn, a historian and journalist with a particular interest in cryptography—brought to mind a concept that those of us who carry firearms for self-defense need to bear in mind as we are bearing arms.
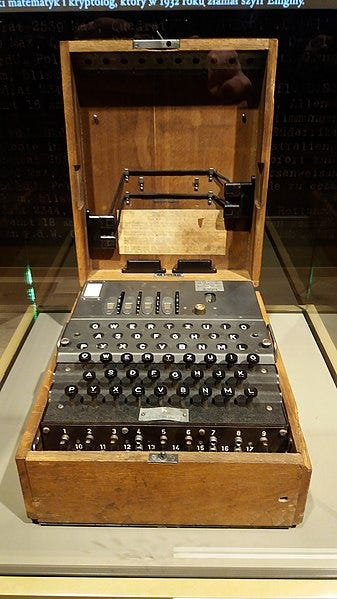
The Enigma machine, a series of devices used by all branches of the German military during the Second World War—though the underlying invention dates back to the Great War and was adopted by elements of the German government in the 1920s—is perhaps best known as the enciphering technology that the geniuses of Bletchley Park cracked—with, in the popular imagination, the aid of gung-ho Americans who captured the U-571. That movie is an abomination that gets right the fact that yes, at various points, there were submarines involved in the Battle of the Atlantic, but little else, especially the truth that the British were the ones who displayed physical courage and intrepidity in multiple operations to capture the machines, manuals, and code books of the German secret communications system. And the reality that it was the Poles who first beat a path to defeating the Enigma before the war even began.
But another reality, one that hides in the background, is that the Enigma was an excellent design for sending messages that only approved recipients could read. The machine made 1.58 X 10^27 distinct settings possible. The product of Bletchley, et al., known to those who needed to do so as Ultra, existed not because the machine itself was bad, but because the human operators were imperfect. German ships sent out into the North Atlantic as weather stations had a simplified version of the encoding system and were poorly protected from British raiders. This allowed the code-breakers to find regularities in messages that acted as a wedge into the heart of more important signals. German radio personnel, being like human beings in boring jobs throughout time, now and then were not careful about changing their message prefixes or in staying up to date in swapping out codes, something akin to contemporary computer users whose password is “PASSWORD” and has been since 1995.
If this sounds like the kind of thing that governments would never do, recall that for two decades during the height of the Cold War, many of the United States’s land-based nuclear missiles had their arming codes—their Permissive Action Links—set to 00000000.
And therein lies the point I wish to elucidate here, namely the recognition that technology may itself be sophisticated in its capacity and broad in its reach, but it is only as good as the grunt or the file clerk or the ham-handed armed citizen using it. That may seem obvious, but let the realization sink in. The lock on a front door may be a complex mechanism that would puzzle Houdini, but if the bracket that receives the bolt is screwed into a piece of pine board, who would bother with picking the tumblers? Or if there is a large window nearby, so much the easier for anyone who wants in.
Nothing is perfect, naturally. Which is to say, a gadget may be flawless in its design, but someone—many somebodies, really—are out there working out ways to get around, over, or through it. Its user may not fully understand it—yes, the point of education and practice is to reduce this deficiency—or may be trying to employ it in ways that are not optimal. This user may be tired, drunk, or ill. Expecting machines to absolve us of the responsibility of planning and decision is a foolish complacency.
I hear this notion brought up frequently in discussions about the accuracy of a particular firearm. The wisdom is that a shooter can bed the action of a rifle, can bolt on lights and lasers and optics that will distinguish the ticks on a deer at five hundred paces, can measure out powder to fractions of a grain, but if said person spends no time learning to put this matter to good use, all the expense is for naught. But the deeper point is that, as the saying goes among people who do battle for a living, the weapon is the warrior. The tools are merely the objects at immediate hand for the warrior to use.
Or, as a corollary, technology is what should be used to delay an attacker long enough for the defender to get into motion. No, the lock on my door will not stop a determined invader for long. Nor will the bar jammed into the knob. But these and other things are there to slow down someone intent on doing me harm, to give me the time to wake up and swing into action. To see the pistol at my side, the brakes in my car, the flash-drive that is a part of my backups for files, and on and on as comprehensive solutions would be to remove myself from moral and actual agency.
There is only one point left to make. If anyone would like to buy me an Enigma replica—a device for which I have no practical use, beyond satisfying a burning covetousness to possess—it may be purchased here.
But buy two of them, since, of course, I would have to give one to the other party in my to-be-secret communications.